Hacking Examples
For example, they may hack into a network without the owner’s permission to search for vulnerabilities. after that, they will usually contact the owner and ask for a small fee to fix the issue. however, if the owner declines, hackers might share their findings online, thus inviting their unethical peers to exploit these vulnerabilities. The 5 worst examples of iot hacking and vulnerabilities in recorded history 1. the mirai botnet (aka dyn attack) back in october of 2016, the largest ddos attack ever was launched on service 2. the hackable cardiac devices from st. jude early last year, cnn wrote, “the fda confirmed that st. jude. 18 proven growth hacking techniques 1 puma. the term growth hacking wasn’t even invented when puma showed its marketing genius in the 1970 world cup finals. 2 dollar shave club. picking a fight with a strong argument is a deadly growth hacking strategy. and mike, the 3 dropbox. dropbox is. Culture hacking: 5 examples you can borrow he’ll do any of your hacking jobs ranging from credit change,grade change,bank account hacks,deleting criminal record e,t,c he also makes original international passport for different countries contact them on bettercredit247@gmail. com and thank me later.
Computer Hacking Methods Examples Of Cyber Criminals
The 20 Biggest Hacking Attacks Of All Time Vpnmentor
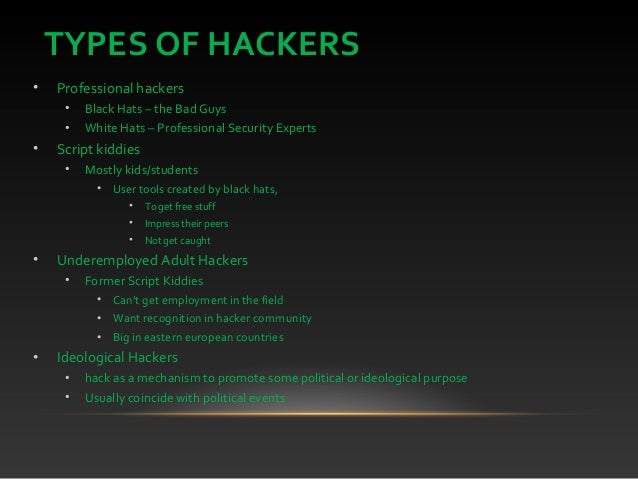
For example, if the source of a river is poisoned, it will hit the entire stretch of animals during summer. in the same way, hackers target the most accessed physical location to attack the victim. Dec 27, 2019 what is hacking? examples and safety tips for 2020. examples of hacking examples different types of hacking. hackers use brute force, security exploits, social engineering, and other means to gain access to systems without proper permission. ethical hacking. hacktivism. identity theft. malware hacking. international espionage.
More hacking examples images. hacking examples 10 hacks that made headlines hacking has been around for decades, starting with curiosity-driven systems break-ins. today's crimes are often financially-motivated fraud. Using simple hacks, a hacker can be able to know about your personal unauthorized information. knowing about these common hacking techniques like phishing, ddos, clickjacking, etc. could come.
19 Growth Hacking Examples That You Can Copypaste Even
Real-world examples koobface. an anagram of facebook, koobface was a hybrid, or blended threat, malware. it used the trickery aspect of a mac flashback. mac flashback attacks almost always occurred without the victim’s knowledge, as apple mac users found out zeroaccess. the zeroaccess rootkit. Iot hacking can be extremely effective, producing ddos attacks that can cripple our infrastructure, systems, and way of life. here are the 5 worst examples. Redirects for a hacking website, fkn0wned, appeared on the steam users' forums, offering "hacking tutorials and tools, porn, free giveaways and much more. " [71] december 14: five members of the norwegian hacker group, noria were arrested, allegedly suspected for hacking into the email account of the militant extremist anders behring breivik. Real-world examples. here are some of the most notorious examples of malware infection, demonstrating the methods and techniques hackers use to penetrate systems. these security breaches have cost computer users inestimable amounts of time, frustration, and money. koobface. an anagram of facebook, koobface was a hybrid, or blended threat, malware.
The list of security hacking incidents covers important and noteworthy events in the history of security hacking and cracking. this was an early example of a kind of sportive, but very effective, debugging that was often repeated in the evolution of apl systems. publication of a hacking instruction manual for penetrating trw credit. Gray hat hacking; gray hat hacking falls somewhere between ethical and unethical. as a rule, gray hat hackers are never outright malicious, though some of their moves could be interpreted as such. for example, they may hack into a network without the owner’s permission to search for vulnerabilities. The top 5 examples softwarelab blog hacking is an umbrella term for a range of activities that aim to compromise computers and networks by exploiting their security vulnerabilities. In the popular meaning of the word gaining access to a computer system or data that a complex subject and there several books on the subject but there can be little things that can be considered hacking for example if you can trick an insider to do what you want or tell you the password (this is so called social hacking) and doesn’t even require advance computer skills, or use a fully devolved software for this (i would call it an evil team-viewer) or just exploit some back doors i once.
What Is Hacking The Top 5 Examples You Need To Know

Top 10 common hacking techniques you should know about.
What Are Examples Of Hacking A Computer Quora
Examples of hacking techniques; how to protect yourself against hacking. if you're not careful, hackers can access your computer . Apr 4, 2019 it's tough hacking examples to gain traction. want to skyrocket your business growth? copy the successful growth hacking examples of netflix, slack, paypal, and .
The history of cybercrime is full of examples of industrial sabotage, although most other examples on hacking examples this list involve angry or rebellious young hackers venting their frustrations on what they see as the evils of big corporations. the spamhaus case is a little different. I’d like to use the ransomware virus as my example here, please do understand though that i’ve never created a ransomware myself so i could be off at some details. first of all, how is the user targeted? generally, hackers that use the ransomware. See more videos for hacking examples.
One example of this is a massive attack against oil firm saudi aramco in 2012, which went completely unreported until details began to leak out several years later. apparently launched via a phishing or spear phishing attack, it gave unknown hackers complete access to the company’s it systems, wreaking havoc on an organisation which controls supply of 10 per cent of the world’s oil. The computer fraud and abuse act, the law that's been at the heart of almost every controversial hacking case of the past decade, is in the news again this month.. prosecutors recently used the.
The list of security hacking incidents covers important and noteworthy events in the history of this was an early example of a kind of sportive, but very effective, debugging that was often repeated in the evolution of apl systems. May 14, 2012 known by the hacker name c0mrade, jonathon james was 16 when, in 1999, he hacked into the marshall space flight center in huntsville, . Grey hat hackers comprise curious people who have just about enough computer language skills to enable them to hack a system to locate potential loopholes in .
Komentar
Posting Komentar