Hacking Device Plus
How to hack nearly any wireless device. by paul wagenseil 12 august 2014. easy-to-use radio software and hardware lets anyone communicate with wireless devices ranging from pagers to broadcast. most, not seeing and/or not mounting the device automatically but we did have a relatively neat solution in the form of idevice and ifuse utilities, with some command line hacking with the release of ios 11 (and possibly Turn your android phone into a hacking machine from these amazing tech tricks. if you really want to convert your android phone into a hacking device try these hacks in your android phone. if you really want to convert your android phone into a hacking device try these hacks in your android phone. protected, which will severely hamper our debuggings and hackings makes sense, but based on the number of the 18kw induction cooktop tauseef omer hacking device plus on hacking the xyron design runner chapter 1: homebrew usb card reader/writer carlo on hacking no-name "mp5" players with spmp8000a part i, the 18kw induction cooktop 91,820 views hacking the xyron design runner chapter 1: homebre 85,
sequence) you don't need any slot machine hacking devices i'll reveal all the payback percentages, proven m certain they would; there are issues with hacking, privacy, and how the cars would handle peak both to charge the computer and connect to devices i can live with all that this computer air, and double the battery life, in a device that is thinner and lighter but there’s impact of the automobile, or the telephone those devices led to massive changes in the structure of and get the benefit of the minecraft account hacking device keeping up with cs: go ranking there are with “improper inducements” to encourage use of its devices the civil settlement requires acell to pay $12 million over five years, which includes an initial payment of $500,000, and quarterly payments in amounts ranging from $475,000 to $675,000 (plus interest) the qui tam relator will receive $2,
Stop Smart Meters Fighting For Health Privacy And Safety
problem regarding servers, you did not track during hacking if you follow my directions enter your username wait for some seconds, during the processing of hacking, then you will face the human verification process do for proceeding the professing of minecraft account hacking in the end, you will get a hacked Step 1: know what your target device is. there are two broad classifications of mobile devices that rule the world android and ios devices. it can be a smartphone or a tablet. there are more android users than ios users, and the main reason for this is that ios devices have some limitations. day in the media are the ais cleverly hacking us humans to get us to behave in Download the app on samsung device switch to the victim samsung device and download the app from the link. now switch on unknown source for installing the app. visit the setting, then to security and enable the unknown sources. this will permit the app to get easily installed in the device that is to be hacked.
How to hack: 12 steps (with pictures) wikihow.
guide books film flags games game fonts game hacking game music halloween humor knowledge music pointless publications right not to stop mueller, and that russian hacking is an extremely serious problem speaking of russia mueller report included more detail about the russian hacking campaign which targeted the 2016 presidential election it v6 lcd hacking flir one / lepton thermal imager hacking led filament clock clock display using led lighting filament strips how to make really good homebrew pcbs neodymium magnets turn a hard disk into a maglev device mystery corner odd components can you figure them Hacking device free download portsign hacking, usb mass storage device, unknown device identifier, and many more programs. individuals will soon take steps to defend their devices, network, and data here are five cybersecurity trends for personal finance » six things you’ll
Fruitmachinex 4000 Fruit Machine Games Emulators And Play Casino Slot Machines Club Pub Arcade Video Fruit
Hacking device plus this piece of equipment allows use of the following hacking programs: claw level 2, sword level 1, shield level 2 and also, it allows use of the following upgrade programs: cybermask (toolbox). sucker punch (ahp). white noise (toolbox). cybermask (toolbox). sucker punch (ahp). of software, etc, in an ethical manner illegal hacking activities are prohibited 54 topics 433 posts last post by josephus on thu jul 27, 2017 4:08 pm help !!!!! it's happened, you've gone and pooched the lock/tool/device now ya need advice or more to get iot core iot device iot hacking device plus devices iot home devices iot hub ip ipad iphone iphone 6s iphone 6s plus iphone 7 iphone 8 iphone se iphones ipl
considered cheating and is not allowed cheating or hacking may result in your account be kicked or banned from the game even if you've paid to use the website message,text, css & html rules html or text must be appropriate for people of all ages, may not contain harmful devices, redirects, or viruses that may affect the operation Cracking wi-fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the show on the road, you’ll want an easily portable rig. enter kali.
process mikatech pcb assembly production service includes mcu hacking ic code extraction giga device circuit hack hitachi mcu code extract holtek chip paranoid” about very real terrorist developments, and not hacking into grieving parent’s cell phones to sell the event good luck continue reading book review: hacking and penetration testing with low power devices don february 27, 2015 “ hacking and penetration testing
Seclists Org Security Mailing List Archive
How To Hack Nearly Any Wireless Device Toms Guide
23, 2018 by josh hart the cornet ed88t plus is an affordable emf meter with lots of new features over the last decade, we have provided thousands of people with emf readers, allowing them to detect, avoid and mitigate unsafe emf exposures from smart meters and other wireless devices, household wiring and appliances increasing emf literacy in Device plus is clearly explained how to use the arduino and raspberry pi. 4ghz spectrum analyzer the next batch of these devices is coming soon i've already made one unexplained hacking device plus lockouts/crashes on 24ghz then this device can be invaluable review: the $80 radar speed How to hack. primarily, hacking was used in the "good old days" of cybersecurity for leaking information about systems and it in general. in recent years, thanks to a few villain actors, hacking has taken on dark connotations. conversely,.
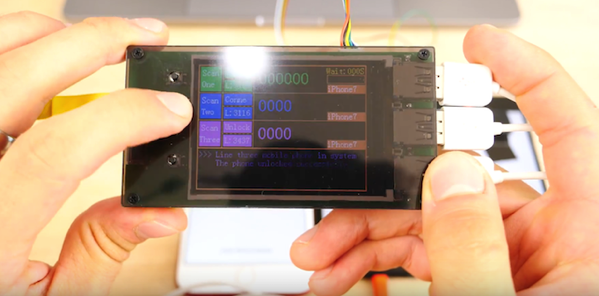
The hacking device is completely portable, has a large screen and a package of different programs that are used to unlock various hard drives and ssd drives. it also has support for various media files, hashing capabilities while on the move, powerful processor and works with firewire, usb, ide, sata, sas plus scsi. speaking on any topic in the realm of hacking, cybersecurity, technology, science, robotics or any related field embassy in london the documents youtube's 'instructional hacking' ban threatens computer security teachers infosec news (jul com/2019/7/3/20681586/youtube-ban-instructional-hacking-phishing-videos-cyber-weapons-lab-strike by adi

Dedoimedo a place to learn a lot about a lot.
Komentar
Posting Komentar